Integrate Azure SAML SSO using Logto
Learn how to integrate Azure SAML SSO using Logto in minutes.
Microsoft Entra ID also known as Azure Active Directory (Azure AD) is a comprehensive identity and access management solution that gives you a robust set of capabilities to manage users and groups. Many organizations use Azure AD to manage their users and groups, and it is also a popular choice for single sign-on (SSO) integration. Auzre AD supports both OpenID Connect (OIDC) and Security Assertion Markup Language (SAML) protocols for SSO integration. In this tutorial, we will show you how to integrate your Logto application with Azure SAML SSO first.
Prerequisites
Before we start, make sure you have an active Azure account. If you don't have one, you can sign up for a free Azure account here.
A Logto cloud account. If you don't have one, you are very welcome to sign up for a Logto account. Logto is free for personal use. All the features are available for dev tenants, including the SSO feature.
A well integrated Logto application is also needed. If you don't have one, please follow the integration guide to create a Logto application.
Integration
Create a new Azure SAML SSO connector in Logto
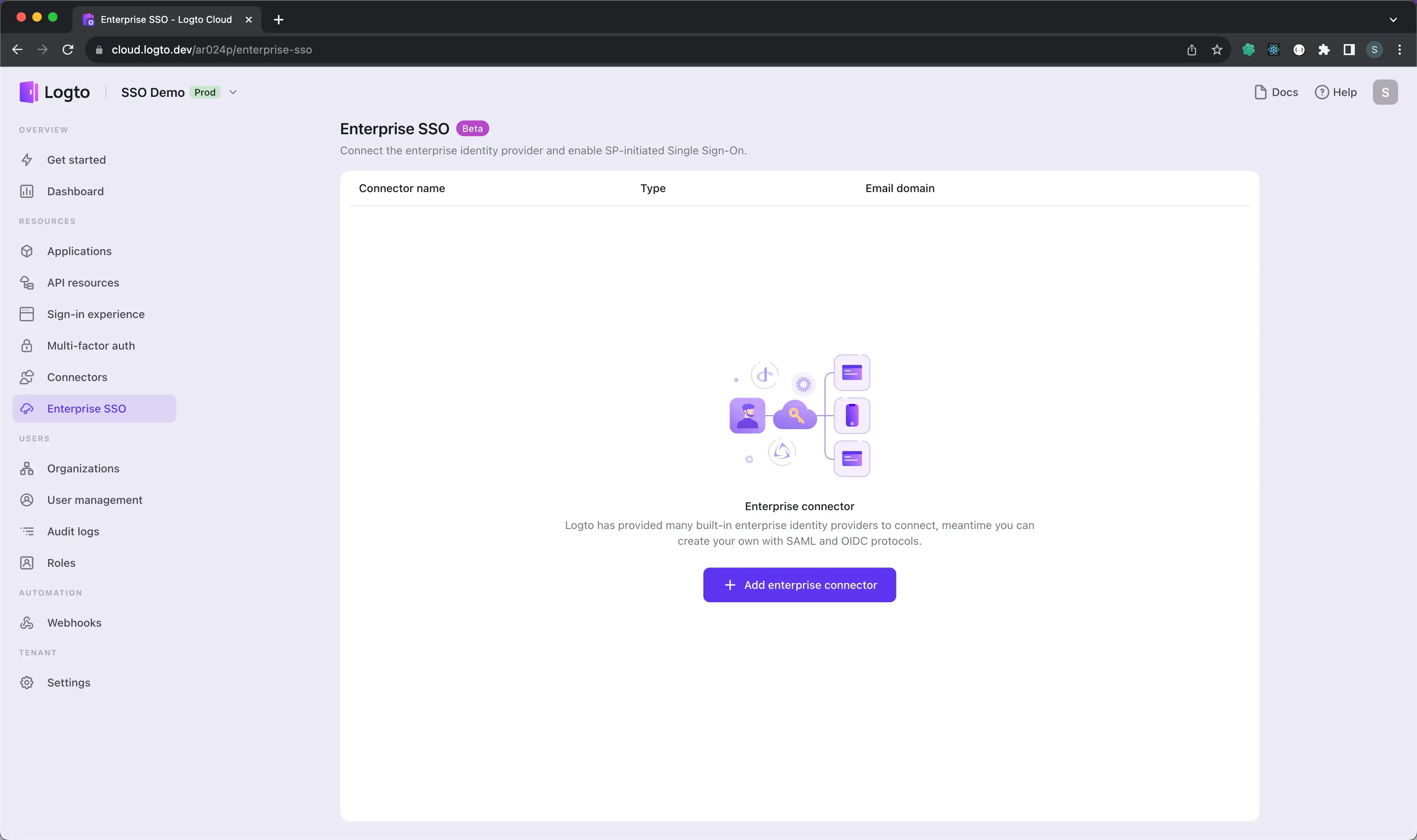
- Visit your Logto Cloud Console and navigate to the Enterprise SSO page.
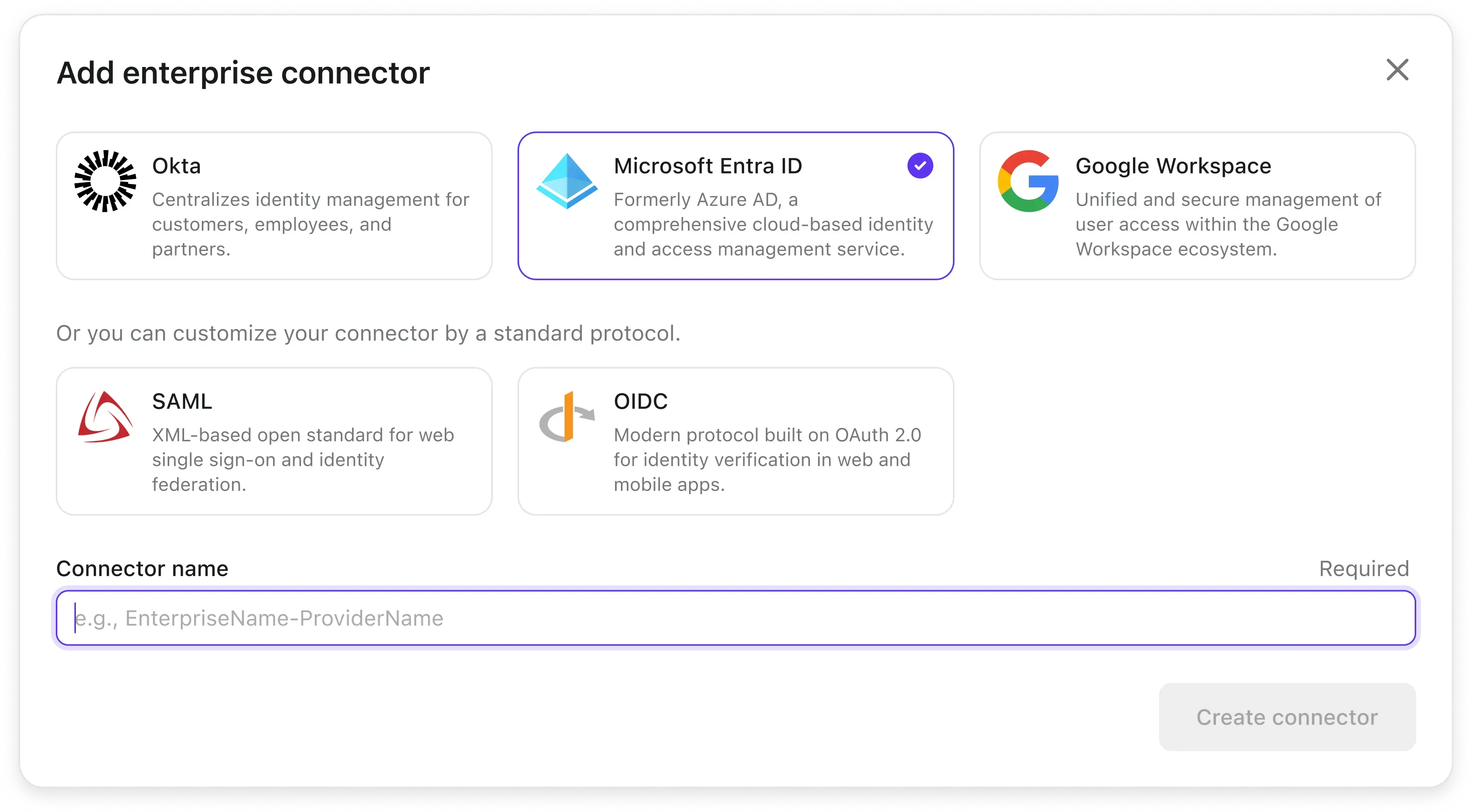
- Click the Add Enterprise SSO button and select Microsoft Enrtra Id (SAML) as the SSO provider.
Let's open the Azure portal in another tab and follow the steps to create an enterprise application on the Azure side.
Create an Azure enterprise application
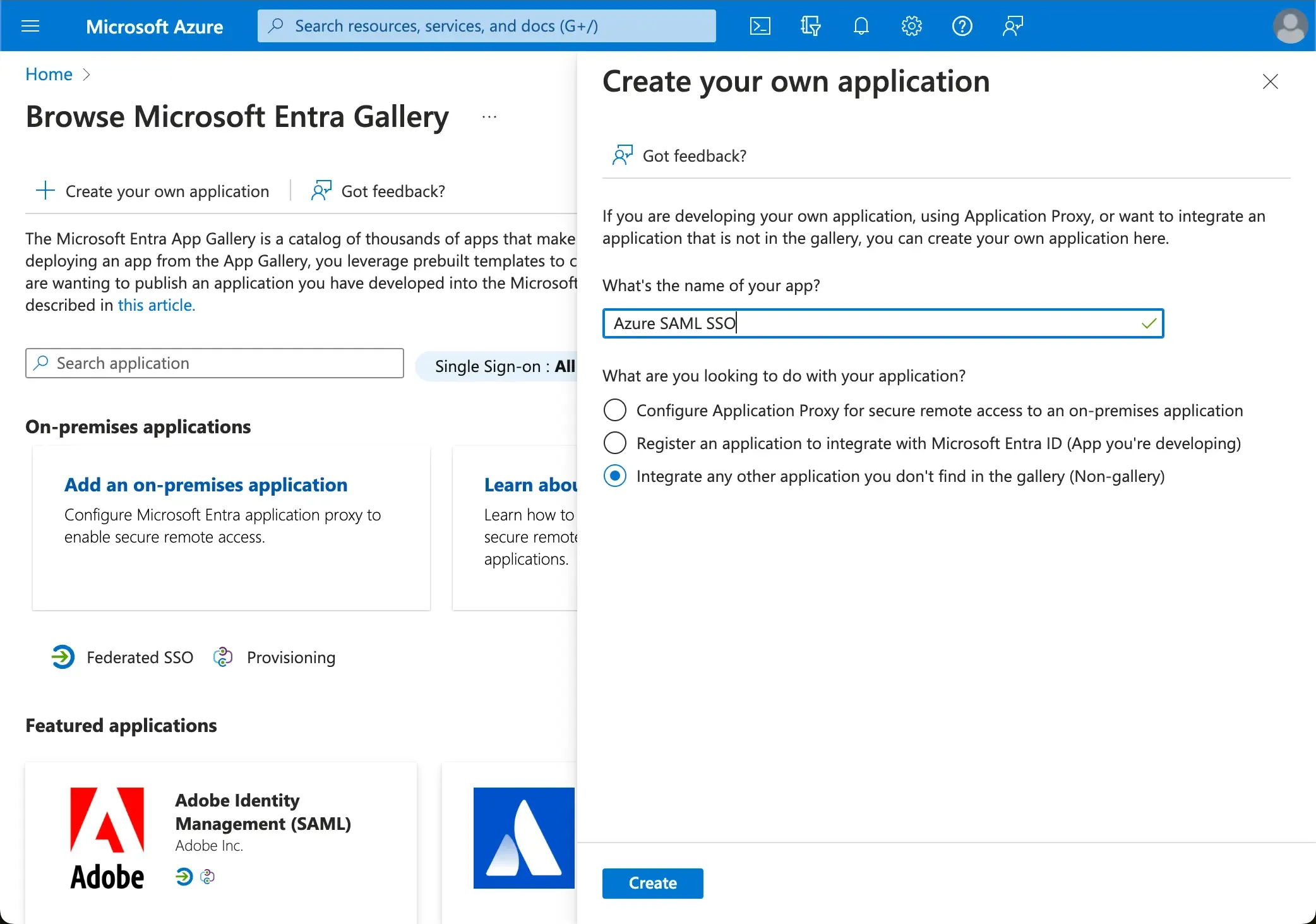
-
Go to the Azure portal and sign in as an administrator.
-
Select
Microsoft Entra IDservice. -
Navigate to the
Enterprise applicationsusing the side menu. ClickNew application, and selectCreate your own applicationon the top menu. -
Enter the application name and select
Integrate any other application you don't find in the gallery (Non-gallery).
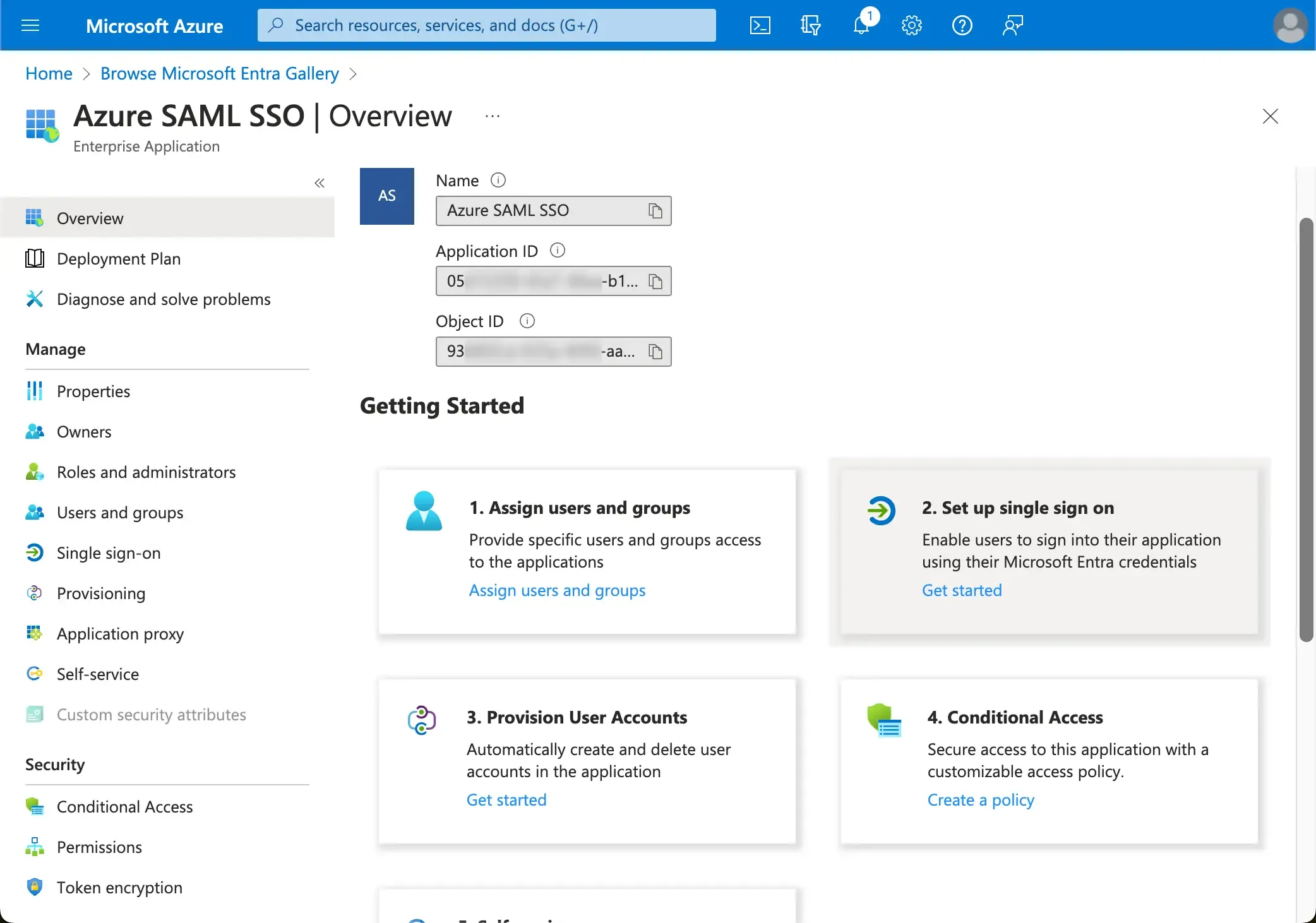
- Once the application is created, select
Setup single sign-on>SAMLto configure the SAML SSO settings.
- Open the first
Basic SAML Configurationsection and copy paste the following information from Logto.
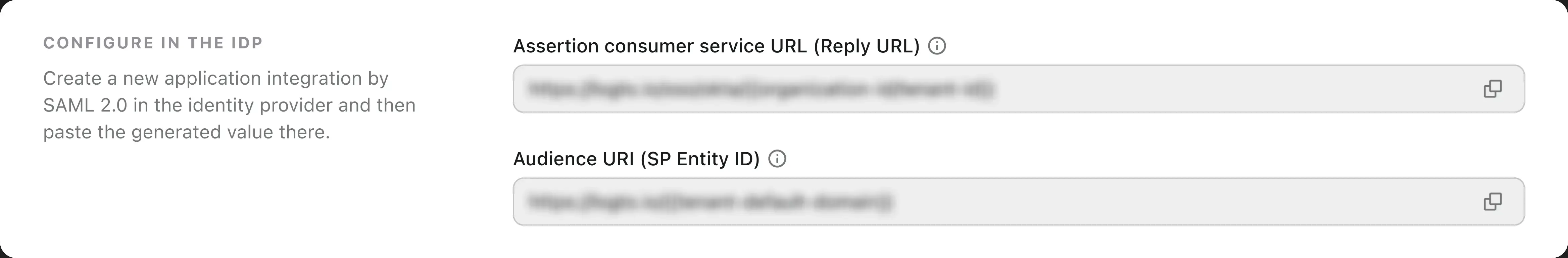
-
Audience URI(SP Entity ID): It represents as a globally unique identifier for your Logto service, functioning as the EntityId for SP during authentication requests to the IdP. This identifier is pivotal for the secure exchange of SAML assertions and other authentication-related data between the IdP and Logto.
-
ACS URL: The Assertion Consumer Service (ACS) URL is the location where the SAML assertion is sent with a POST request. This URL is used by the IdP to send the SAML assertion to Logto. It acts as a callback URL where Logto expects to receive and consume the SAML response containing the user's identity information.
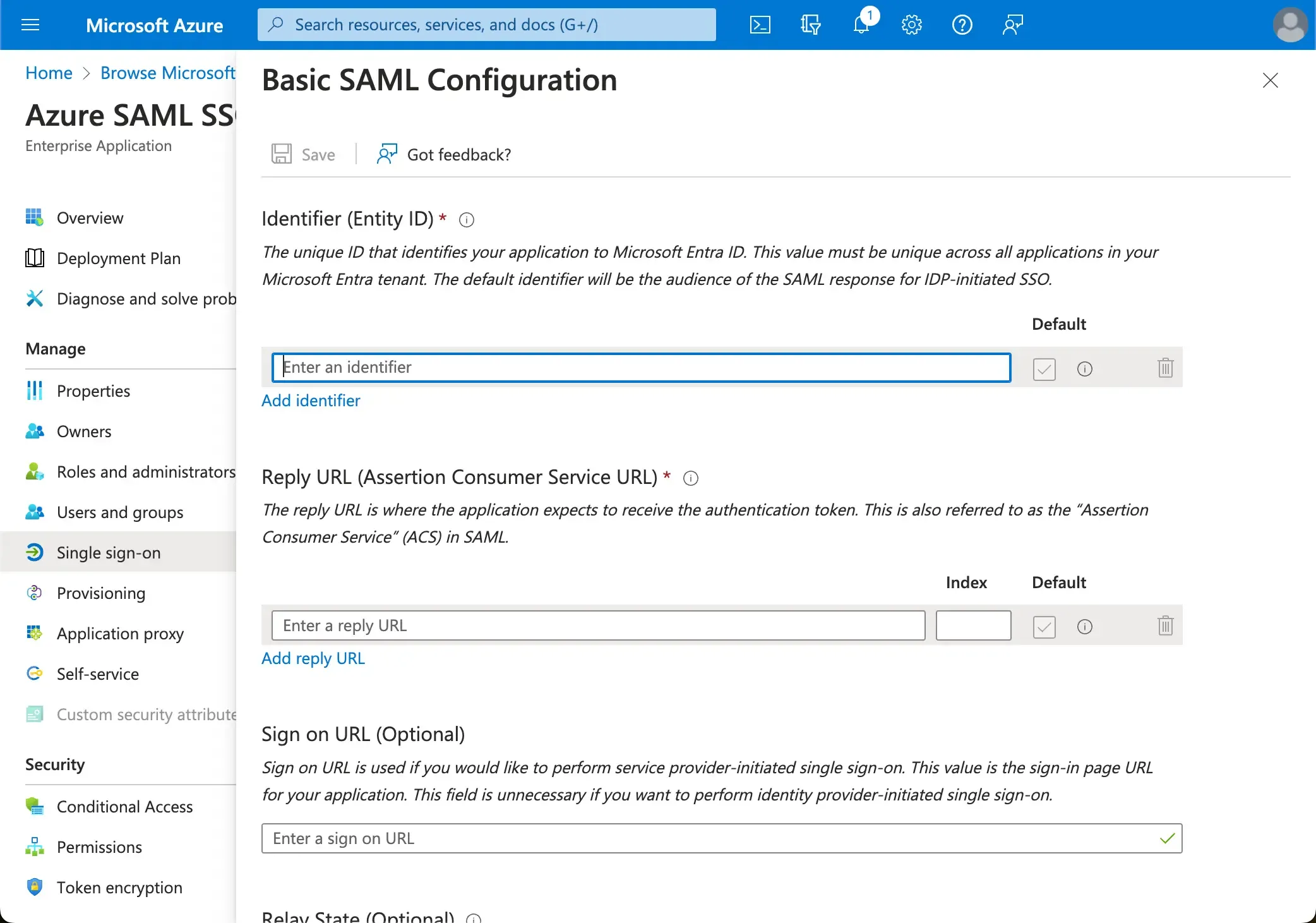
Click Save to save the configuration.
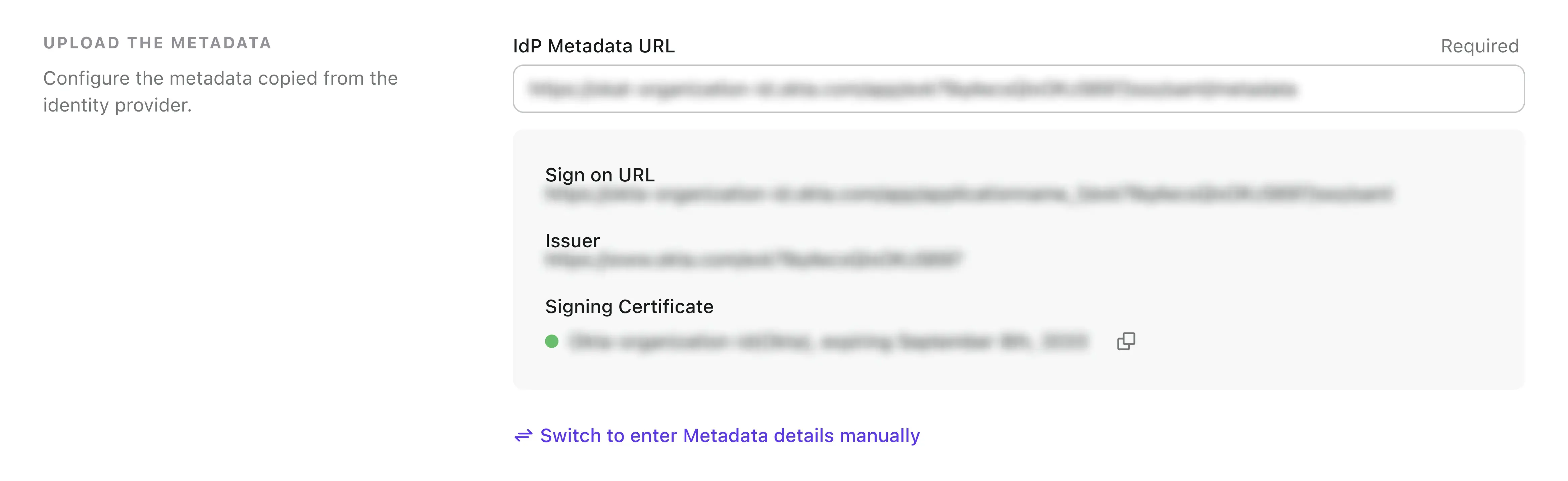
Provide the SAML IdP metadata to Logto
Once the SAML SSO application is created in Azure, you will provide the SAML IdP metadata configuration to Logto. The metadata configuration contains the SAML IdP's public certificate and the SAML SSO endpoint.
-
Logto provides three different ways to configure the SAML metadata. The easiest way is through the metadata URL. You can find the metadata URL in the Azure portal.
Copy the
App Federation Metadata Urlfrom your Azure AD SSO application'sSAML Certificates sectionand paste it into theMetadata URLfield in Logto.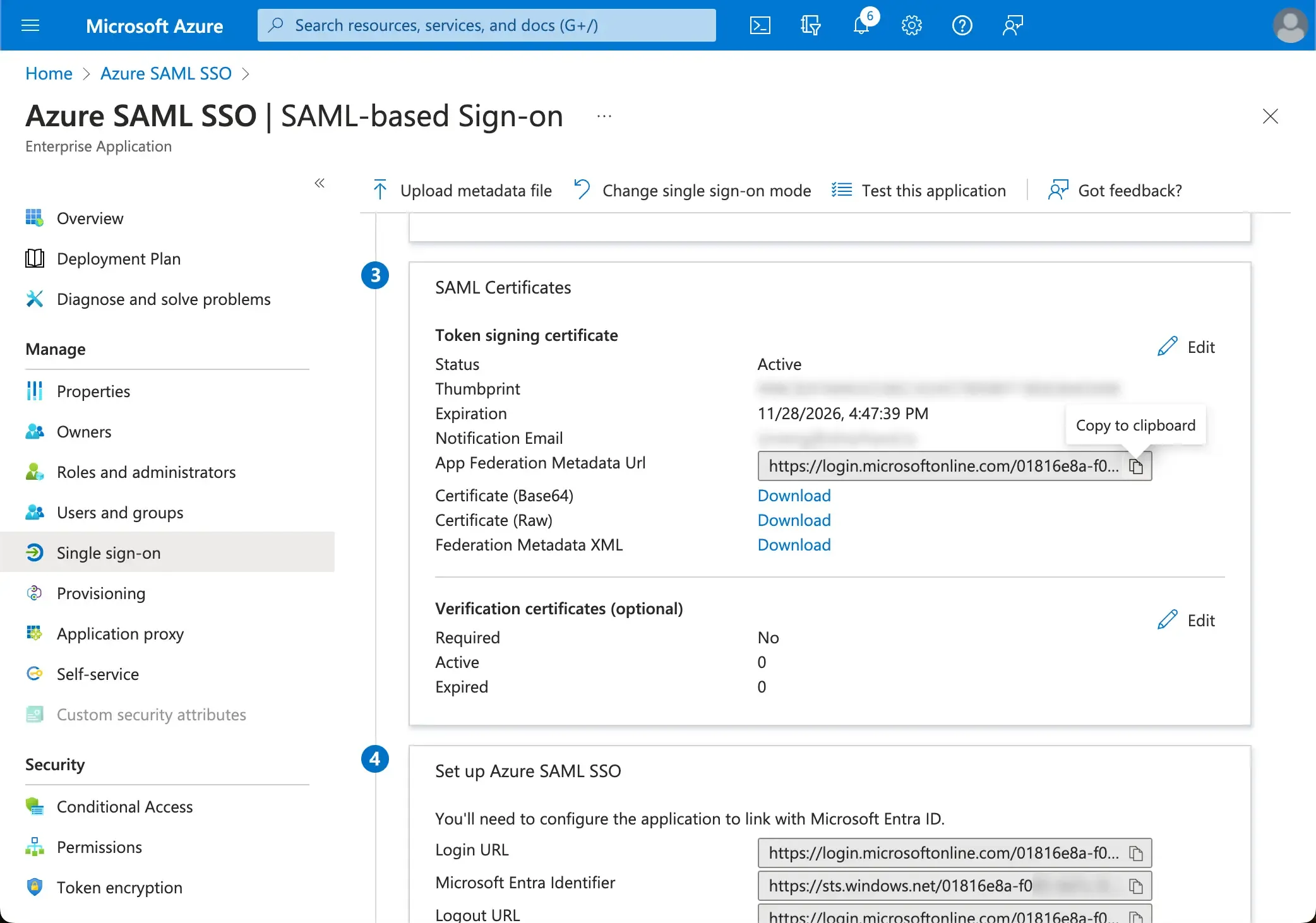
-
Click on the save button and Logto will fetch the metadata from the URL and configure the SAML SSO integration automatically.
Config the user attribute mapping
Logto provides a flexible way to map the user attributes returned from IdP to the user attributes in Logto.The following user attributes from IdP will be synced to Logto by default:
- id: The unique identifier of the user. Logto will read the
nameIDclaim from the SAML response as the user SSO identity id. - email: The email address of the user. Logto will read the
emailclaim from the SAML response as the user primary email by default. - name: The name of the user.
You may manage the user attributes mapping logic either on the Azure AD side or Logto side.
-
Map the AzureAD user attributes to Logto user attributes at Logto side.
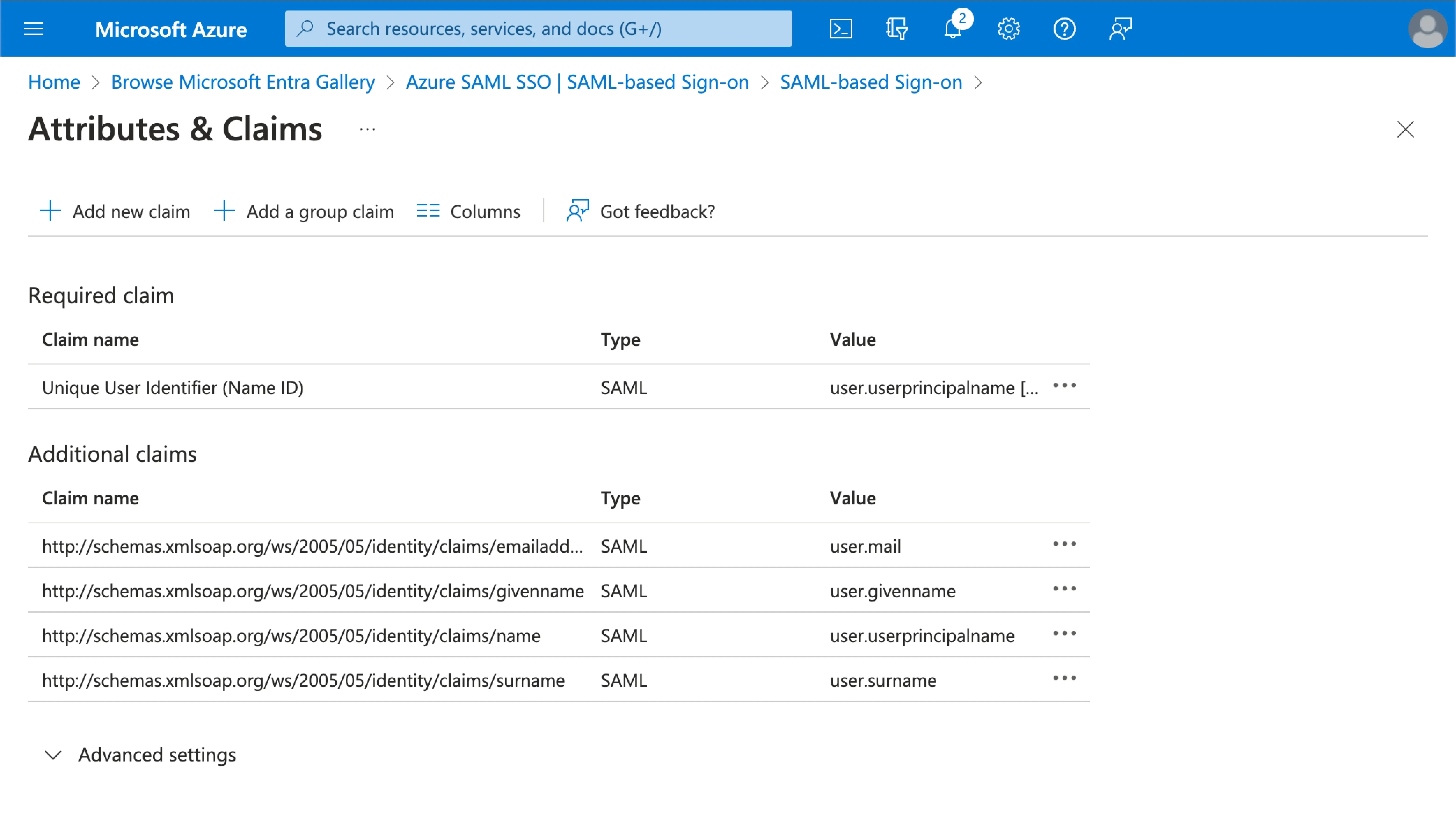
Visit the
Attributes & Claimssection of your Azure AD SSO application.Copy the following attribute names (with namespace prefix) and paste them into the corresponding fields in Logto.
-
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/emailaddress -
http://schemas.xmlsoap.org/ws/2005/05/identity/claims/name(Recommendation: update this attribute value map touser.displaynamefor better user experience)
-
-
Map the AzureAD user attributes to Logto user attributes at AzureAD side.
Visit the
Attributes & Claimssection of your Azure AD SSO application.Click on
Edit, and update theAdditional claimsfields based on the Logto user attributes settings:- update the claim name value based on the Logto user attributes settings.
- remove the namespace prefix.
- click
Saveto continue.
Should end up with the following settings:
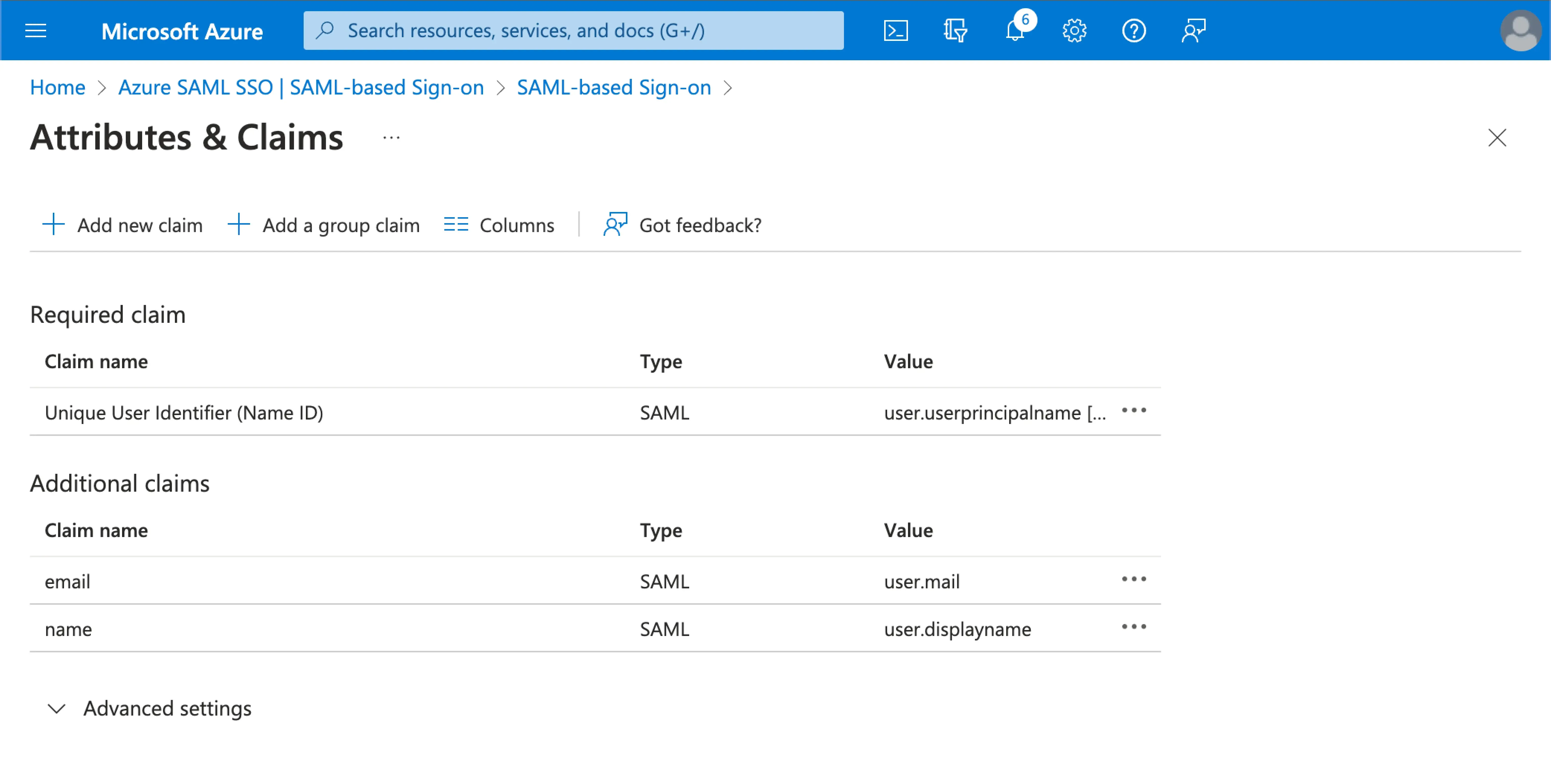
You may also specify additional user attributes on the Azure AD side. Logto will keep a record of the original user attributes returned from IdP under the user's sso_identity field.
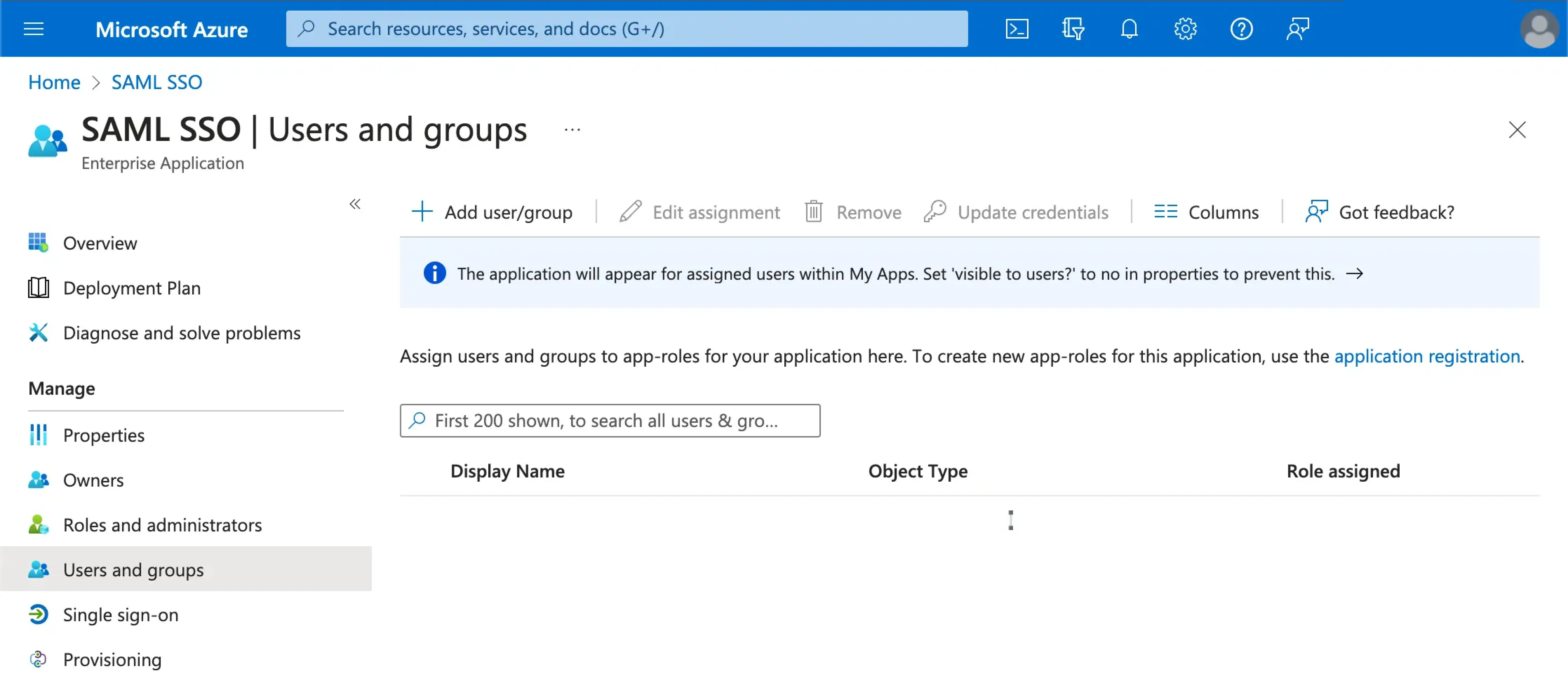
Assign users to the Azure SAML SSO application
You will need to assign users to the Azure SAML SSO application to enable the SSO experience for them.
Visit the Users and groups section of your Azure AD SSO application. Click on Add user/group to assign users to the Azure AD SSO application. Only users assigned to your Azure AD SSO application will be able to authenticate through the Azure AD SSO connector.
Enable the Azure SAML SSO connector in Logto
Set email domain and enabled the Azure SAML SSO connector in Logto
Provide the email domains of your organization at the Logto's SAML SSO connector experience tab. This will enable the SSO connector as an authentication method for those users.
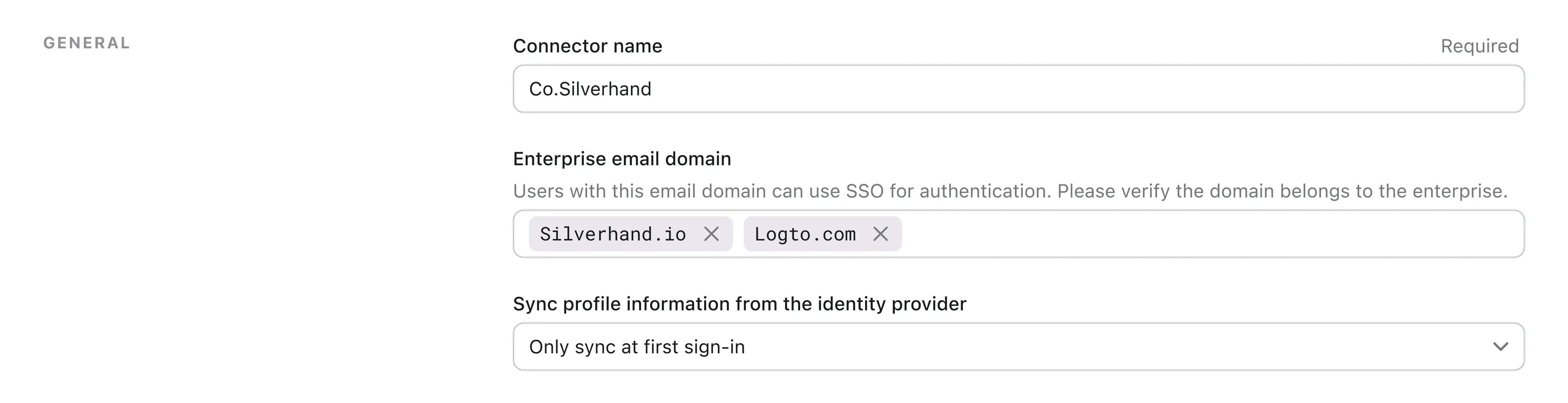
Users with email addresses in the specified domains will be exclusively limited to use SAML SSO connector as their only authentication method.
Enable the Azure SAML SSO connector in Logto's sign-in experience
Go the Sign-in Experience tab and enable the enterprise SSO.
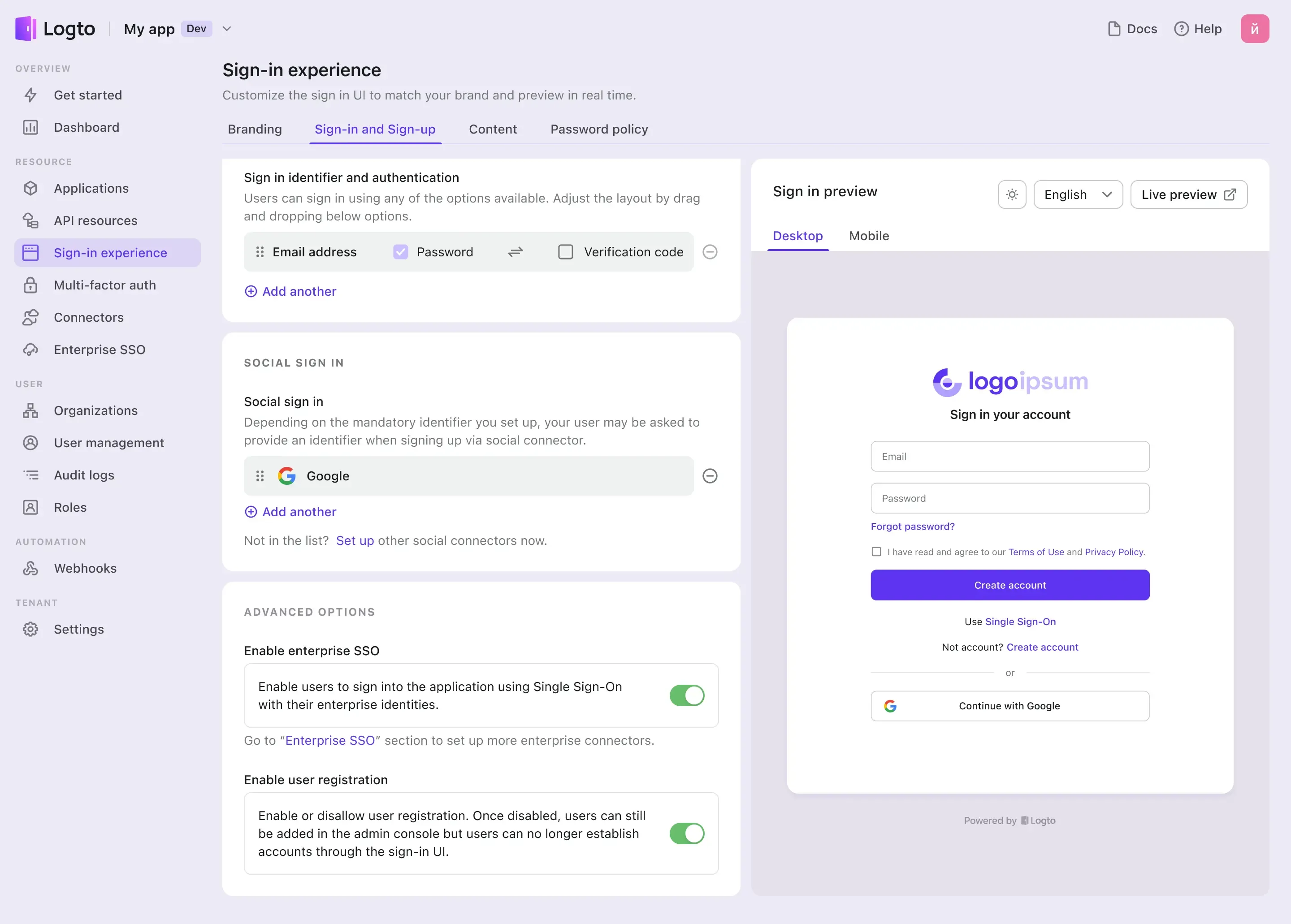
Now, you may test the SSO integration by using the live preview button at the top right corner of the Sign-in Experience preview section.

