Logto product updates
🎉 Introducing our March release: Create your ideal sign-up flow with multiple identifiers, connect with WordPress in minutes, and explore more updates!
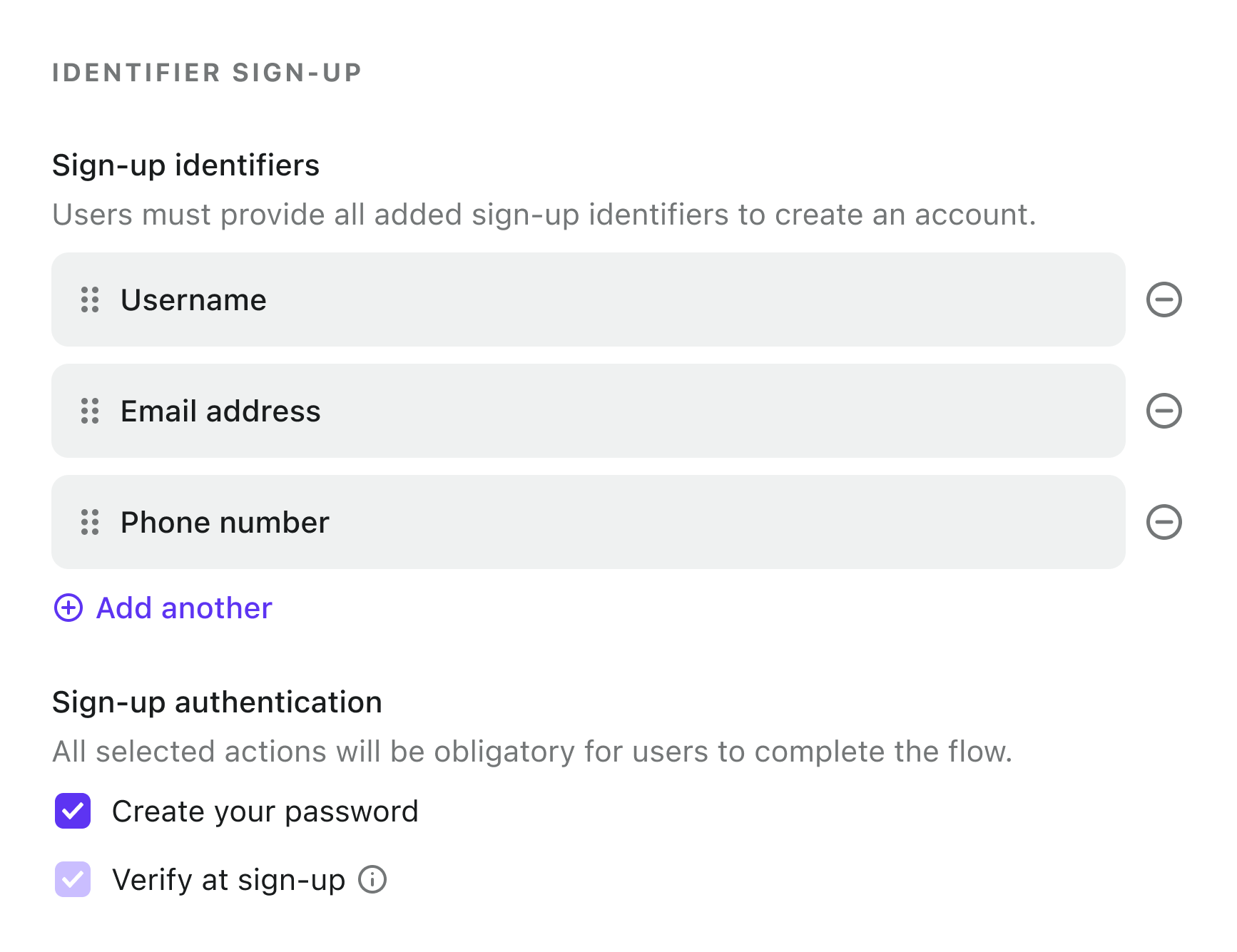
Support multiple sign-up identifiers
Logto now supports configuring multiple required identifiers for user registration. This enhancement extends the previous single-identifier limitation, enabling a more comprehensive sign-up process.
Sign-in experience schema
Introduces a new optional field, secondaryIdentifiers, to the sign-in experience sign-up settings. This enhancement allows developers to specify multiple required user identifiers during the user sign-up process. Available options include email, phone, username and emailOrPhone.
The difference between sign-up identifiers
Primary identifiers (signUp.identifiers):
- Maintains backward compatibility with existing sign-in experience settings
- Represents the initial registration form
- Uses OR logic: Only one type of identifier will be collected
- Special case:
[email, phone]allows either email OR phone registration, treated as a single requirement.
Secondary identifiers (SignUp.secondaryIdentifiers):
- New field introduced for multi-identifier support
- Collects additional required identifiers after primary registration
- Uses AND logic: all configured identifiers are mandatory
- Supports
emailOrPhonetype: requires either email OR phone, treated as a single requirement
Examples:
Example 1: Username with required email and phone
- Primary:
username - Secondary:
emailandphone
Example 2: Username with either email or phone
- Primary:
username - Secondary:
emailOrPhone
Example 3: Email/phone with required username
- Primary:
emailORphone - Secondary:
username
Console updates
Enhanced sign-up configuration UI:
- Introduced a multi-selector interface replacing the previous single-identifier selector
- Added drag-and-drop functionality for prioritizing identifiers
- The first identifier in the list serves as the primary identifier (
signUp.identifiers) - Subsequent identifiers are stored as secondary identifiers (
signUp.secondaryIdentifiers)
Enhanced sign-in experience configuration
We've relaxed several configuration constraints to give you more flexibility in customizing your authentication flows.
-
The password requirement is now optional when using
usernameas a sign-up identifier. Please note, when configuringusernameas the sole sign-up identifier with password disabled, users will be unable to authenticate after registration. Ensure at least one of the following:- Enable password requirement at sign-up
- Configure additional sign-up identifiers
-
Removed the constraint requiring sign-up identifiers to be enabled as sign-in methods. We have fully decoupled the sign-up identifier settings from the sign-in methods. Developers can now require as many user identifiers as needed during the sign-up process without impacting the sign-in process.
-
Removed the requirement for password verification across all sign-in methods when password is enabled for sign-up.
Experience package updates
In this release, we have transitioned the user sign-in experience from the legacy @logto/experience-legacy package to the latest @logto/experience package. This change fully adopts our new Experience API, enhancing the underlying architecture while maintaining the same user experience.
- The sign-in experience front-end now uses the
@logto/experiencepackage by default. - Fully adopts our new Experience API for improved performance and maintainability
- Maintains complete feature parity with no visible changes to end-users
- Legacy Interaction API and
@logto/experience-legacywill be deprecated in future releases.
CLI updates
@logto/translate
-
Improve the OpenAI prompt to better support i18n plural form suffixes
-
make method
isLanguageTagcase-insensitiveLanguage tag case inconsistency was causing translation mismatches across packages:
@logto/phrasesand@logto/phrases-experience: using lowercase tags (e.g.,pt-br,zh-cn)@logto/language-kit: using mixed-case tags (e.g.,pt-BR,zh-CN)
Updated
isLanguageTagfunction in language kit to be case-insensitive, ensuring:- Consistent language tag matching regardless of case
- Proper detection of all language tags by translate CLI tool
- Fixed missing translations due to case mismatches
Logto integrations updates
- WordPress integration guide: Added out-of-box WordPress plugin integration documentation to Logto console
- Azure AD social connector enhancement: Added OAuth
scopesfield to@logto/connector-azuread- Enables customization of requested user permissions
- Provides greater flexibility in access control
- OIDC SSO connector authentication bug fixes: Removed
client_idfrom token request body- Resolves compatibility issues with OIDC providers like Okta
- Eliminates redundant client authentication method
- Before:
client_idincluded in both request body and authentication header - After: Uses authentication header only
- Before:
- This OIDC SSO connector update improves compatibility with providers that enforce strict client authentication methods. By removing the redundant
client_idfrom the request body while maintaining the authentication header, we ensure consistent behavior across different OIDC providers.

