Logto product updates (2024 July)
Last month we introduced a loooot of new features and improvements. We also have big news about compliance to share.
Compliance
We are SOC 2 Type I compliant, officially! 🎉 A Type II audit is on the horizon.
Just-in-Time provisioning for organizations
This feature allows users to automatically join the organization and be assigned roles upon their first sign-in through some authentication methods. You can set requirements to meet for Just-in-Time provisioning.
To use this feature, head to the organization settings and find the "Just-in-Time provisioning" section. Management APIs are also available to configure this feature via routes under /api/organizations/{id}/jit. To learn more, see Just-in-Time provisioning.
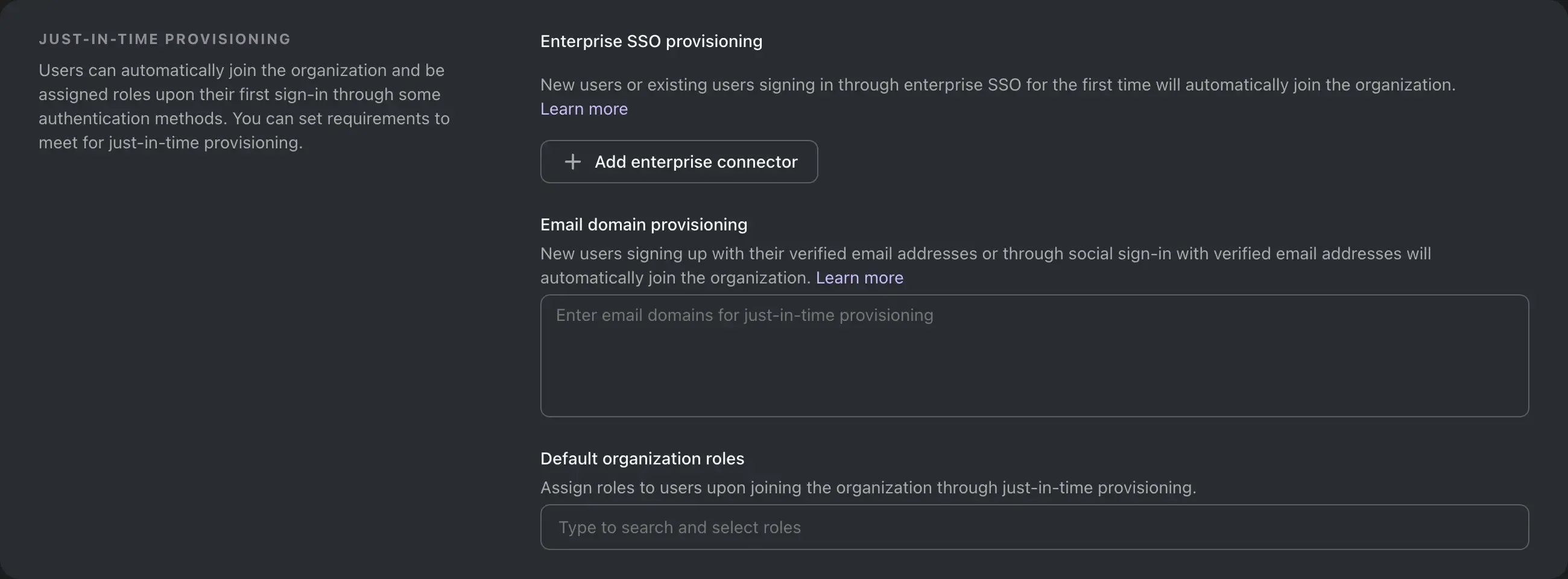
Email domains
New users will automatically join organizations with Just-in-Time provisioning if they:
- Sign up with verified email addresses, or;
- Use social sign-in with verified email addresses.
This applies to organizations that have the same email domain configured.
Click to expand
To enable this feature, you can add email domain via the Management API or the Logto Console:
- We added the following new endpoints to the Management API:
GET /organizations/{organizationId}/jit/email-domainsPOST /organizations/{organizationId}/jit/email-domainsPUT /organizations/{organizationId}/jit/email-domainsDELETE /organizations/{organizationId}/jit/email-domains/{emailDomain}
- In the Logto Console, you can manage email domains in the organization details page -> "Just-in-Time provisioning" section.
SSO connectors
New or existing users signing in through enterprise SSO for the first time will automatically join organizations that have Just-in-Time provisioning configured for the SSO connector.
Click to expand
To enable this feature, you can add SSO connectors via the Management API or the Logto Console:
- We added the following new endpoints to the Management API:
GET /organizations/{organizationId}/jit/sso-connectorsPOST /organizations/{organizationId}/jit/sso-connectorsPUT /organizations/{organizationId}/jit/sso-connectorsDELETE /organizations/{organizationId}/jit/sso-connectors/{ssoConnectorId}
- In the Logto Console, you can manage SSO connectors in the organization details page -> "Just-in-Time provisioning" section.
Default organization roles
You can also configure the default roles for users provisioned via this feature. The default roles will be assigned to the user when they are provisioned.
Click to expand
To enable this feature, you can set the default roles via the Management API or the Logto Console:
- We added the following new endpoints to the Management API:
GET /organizations/{organizationId}/jit/rolesPOST /organizations/{organizationId}/jit/rolesPUT /organizations/{organizationId}/jit/rolesDELETE /organizations/{organizationId}/jit/roles/{organizationRoleId}
- In the Logto Console, you can manage default roles in the organization details page -> "Just-in-Time provisioning" section.
Machine-to-machine apps for organizations
This feature allows machine-to-machine apps to be associated with organizations, and be assigned with organization roles.
OpenID Connect grant
The client_credentials grant type is now supported for organizations. You can use this grant type to obtain an access token for an organization.
Click to expand Console updates
- Add a new "machine-to-machine" type to organization roles. All existing roles are now "user" type.
- You can manage machine-to-machine apps in the organization details page -> Machine-to-machine apps section.
- You can view the associated organizations in the machine-to-machine app details page.
Click to expand Management API updates
A set of new endpoints are added to the Management API:
/api/organizations/{id}/applicationsto manage machine-to-machine apps./api/organizations/{id}/applications/{applicationId}to manage a specific machine-to-machine app in an organization./api/applications/{id}/organizationsto view the associated organizations of a machine-to-machine app.
Swagger (OpenAPI) improvements
Build operationId for Management API in OpenAPI response
As per the specification:
operationIdis an optional unique string used to identify an operation. If provided, these IDs must be unique among all operations described in your API.
This greatly simplifies the creation of client SDKs in different languages, because it generates more meaningful function names instead of auto-generated ones, like the following examples:
Fixed OpenAPI schema returned by the GET /api/swagger.json endpoint
- The
:character is invalid in parameter names, such asorganizationId:root. These characters have been replaced with-. - The
tenantIdparameter of the/api/.well-known/endpoints/{tenantId}route was missing from the generated OpenAPI spec document, resulting in validation errors. This has been fixed.
Backchannel logout support
We've enabled the support of OpenID Connect Back-Channel Logout 1.0.
To register for backchannel logout, navigate to the application details page in the Logto Console and locate the "Backchannel logout" section. Enter the backchannel logout URL of your RP and click "Save".
You can also enable session requirements for backchannel logout. When enabled, Logto will include the sid claim in the logout token.
For programmatic registration, you can set the backchannelLogoutUri and backchannelLogoutSessionRequired properties in the application oidcClientMetadata object.
Sign-in experience
Support Google One Tap
When you added Google as a social connector, you can now enable Google One Tap to provide a smoother sign-in experience for your users with Google accounts.
Head to the Google connector settings in the Logto Console and switch on the "Google One Tap" option.
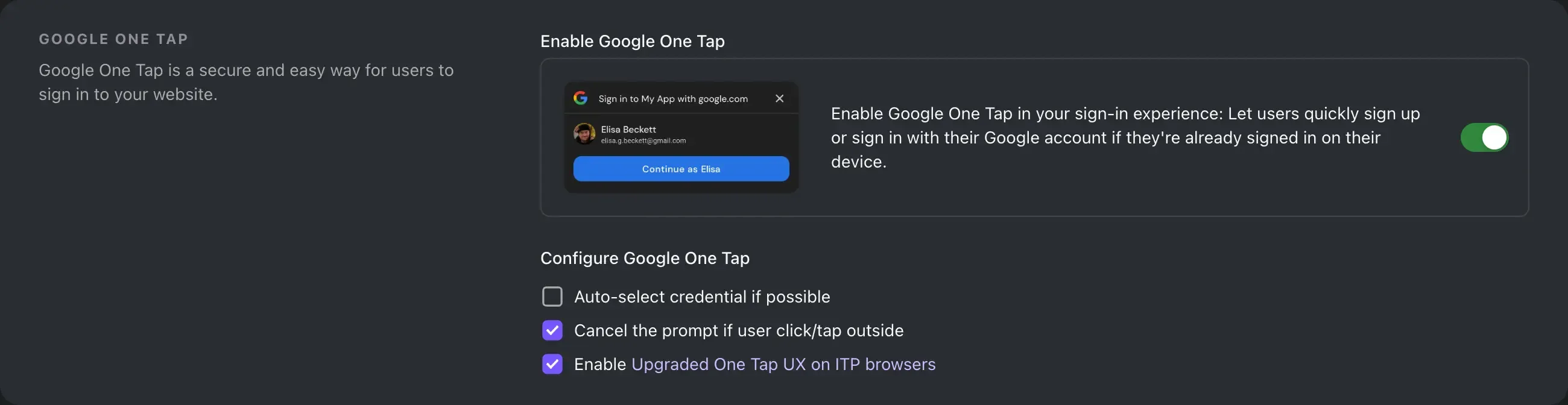
To learn more about Google One Tap, see Enable Google One Tap.
Allow skipping manual account linking during sign-in
You can find this configuration in Console -> Sign-in experience -> Sign-up and sign-in -> Social sign-in -> Automatic account linking.
When switched on, if a user signs in with a social identity that is new to the system, and there is exactly one existing account with the same identifier (e.g., email), Logto will automatically link the account with the social identity instead of prompting the user for account linking.
Agree to terms polices for sign-in experience
We've added a new configuration to allow you to set the terms of service agreement policy for sign-in experience:
- Automatic: Users automatically agree to terms by continuing to use the service.
- ManualRegistrationOnly: Users must agree to terms by checking a box during registration, and don't need to agree when signing in.
- Manual: Users must agree to terms by checking a box during registration or signing in.
Console improvements
- Added Ruby and Chrome extension guide.
- Display OIDC issuer endpoint in the application details form.
- Application guides have been reorganized to provide a better developer experience.
- Now you can view and update user's
profileproperty in the user settings page. - Improved machine-to-machine application integration user experience.
- Fixed a regression bug that error toasts pop up in audit log when logs are associated with deleted applications.
Other improvements
- Added
hasPasswordto custom JWT user context. - Connector: Google and Azure AD connectors now support custom
prompt. - Support per-organization multi-factor authentication requirement:
- An organization can now require its member to have multi-factor authentication (MFA) configured. If an organization has this requirement and a member does not have MFA configured, the member will not be able to fetch the organization access token.
- A dev panel is available after you sign in to the live preview.
- Pagination is now optional for
GET /api/organizations/{id}/users/{userId}/roles. If you don't providepageandlimitquery parameters, the API will return all roles. - Added user detail data payload to the
User.Deletedwebhook event.

